Is your WordPress site infected with malware? It can be extremely headache to deal with. Scanning and cleanup a hacked site isn’t a simple task. There are many things involved and many techniques required to get it done properly. But sometimes, if a site is just slighted infected, cleaning up the malicious code and infected file isn’t as difficult as you may think.
I happen to have a site like this recently. It didn’t take me too long to identify the infected files and cleanup the site. It is a very good example to demonstrate some basic skills and steps to cleanup malware from infected WordPress site. Hope it could give you some ideas, and help you in your battle fighting malware.
Background about this job is not complicated as well. Client was warned by hosting company that, his site was infected. He is a regular WordPress user, no coding knowledge whatsoever. His site was recently soft launched, and he did the most front-end customization.
You may wonder why I didn’t scan & cleanup using plugin or other tools. Well, first of all, I have my own “secret way” to handle it as initial investigation. Secondly, the famous Sucuri online scan tool found the site was clean, “No Malware Detected by External Scan”.
In fact, the site was infected with Pharma Hack. A random link on different page is displayed on top of the navigation menu. Here is a screenshot:
[Update on Jan 15, 2015] Matter of fact, I have another client today because his site was infected. It is confirmed to be the same malware after my initial inspection. The “extra” link on the website looks like this:
(Both sites are hosted by the same hosting company. To Sucuri, the second site is also “Clean”.)
Identify Infected File
I normally start looking for infected files in active theme folder (and subfolders). Then move onto plugin folders. The most common infected files in the theme folder to check out should be: header.php, footer.php and function.php. Because these files will be executed on every page load. It make sense to embed the malicious code in these files. The key is to look at the last modification time stamp.
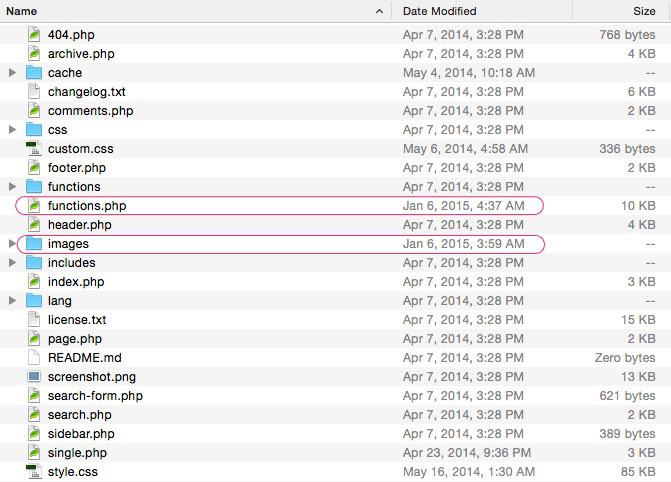
This is the screenshot of theme root folder. The suspicious file & folder are marked out in red.
The majority files and folders have a time stamp of “Apr 7, 2014”. Anything other than this date should raise an alert.
Checking the source code of functions.php proved my conjecture. Here is what inside function.php.
To cleanup, the best way is to replace infected file (function.php) with a safe copy from proven clean source, either the original theme package or known good backup. Tracking the client’s site backups back to one month ago, the file was still infected. I simply cleanup the file by removing the malicious code from beginning up to the “WooThemes functions” comment.
Backdoor Hiding in Image Folder
Hiding backdoor files in image folder is another common hack. These backdoor files are not loaded by regular web browsing but give hackers the possibility to gain access to your website freely. If backdoor files are not cleaned up thoroughly, a site will likely be infected again.
Refer to the first screenshot, there is something abnormal in images folder, and we need to check it out. Here is what’s in there:
There is no business for a PHP script staying in an image folder. This hacker tried to hide the file using a file name similar to existing files. But it is sold by the modification date. DELETE IT!
Not limited to images folder, hackers just try to hide backdoor in any folder possible through the whole site. Complete scanning is required to make sure the website is 100% cleaned up.
Instead of going through folder by folder, one trick is using a file search tool, for example, Windows File Explorer, to locate the malicious files quickly. By doing so, I found few other backdoor files hidden in various subfolders.
Final Cleanup
As I mentioned, this is just my initial investigation. Even the website may look and behave normally again and malicious files can not be found manually, this should not be the end of the process.
I then go through few different way to scan the infected site again, and few more times in the following days.
Final Thoughts
Finding and cleanup malware infected site is just the beginning, a new start of another battle between the hacker and you, the site owner. From this simple example, we can find some interesting facts and apply them in our overall website security practice.
- Update plugins regularly
When WordPress update plugin, it first downloads the latest package from the source (e.g. wordpress.org public repository). Followed by removing old version plugin folder, extracting the new version from the package, moving it into position, and reactivate it.
So, updating plugins is actually a reassurance that you have a clean copy of the plugin. If you are not sure a plugin is clean, delete and re-install it again. - Update theme regularly
Get rid of the habit of working on the theme, and start using child theme. It is really easy to update (or replace) the parent theme when possible or required.
Keep a up-to-date child theme backup copy handy. - Delete unused plugins & themes
If a plugin or theme is not being used by the website, it is easy to ignore them. But it also can be a target for hackers to hide their backdoor files. DELETE it. - Backup, and verify backup regularly
Restoring from the latest backup is my favorite solution to cleanup a malware infected website. Of course, the backup must be clean. Sometimes, the site has been infected for a while and you may not know it. In such case, backup can also be infected.
Scan the backup before restore, especially when the restore is to clean up a hacked site.